I once heard a joke that went something like this: At the sunday church service,…
They said they were sorry. They’re not!
I checked my spam folder this morning (as we should all do from time to time) and – as usual – there were a bunch of the usual extortion attempts. They often start out with:
“I am sorry to inform you that your device was compromised. I’ll explain what led to all of this. I have used a Zero Day vulnerability with a special code to infect your device through a website. This is a complicated software that requires precise skills that I have. It works as a chain with specially crafted and unique code and that’s why this type of an attack can go undetected. You only need one not patched vulnerability to be infected, and unfortunately for you – it works that simple.”
They go on to say that they’ve captured video footage of me doing some nefarious things on my webcam which – if true – would be an amazing technological achievement for them considering that I don’t have a webcam!
And as usual they ask for payment in bitcoin to “make the problem go away”.
If you ever get any of these types of eMails, just delete them. They’re 100% fake – even the ones that appear to come from your own eMail address – and even the ones that may include one of your passwords.
There’s a 2 part message that I wanted to get across here:
(1) If a scammer refers to one of your passwords in their eMail then it almost certainly means that one of the websites that you have an account with has been compromised and your details leaked (“pwned” is the technical term for it). The easiest way to check is to pop along to https://haveibeenpwned.com/ – enter your address(es) – and see which site(s) had the breach. One thing to remember; if your address has been pwned it’s important to change your password on EVERY site that used that password – not just the one that had the leak. I can’t stress that highly enough.
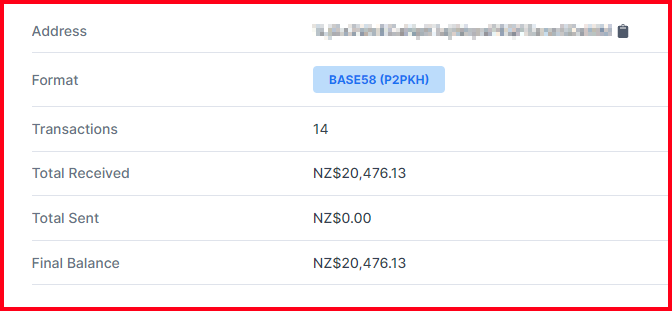
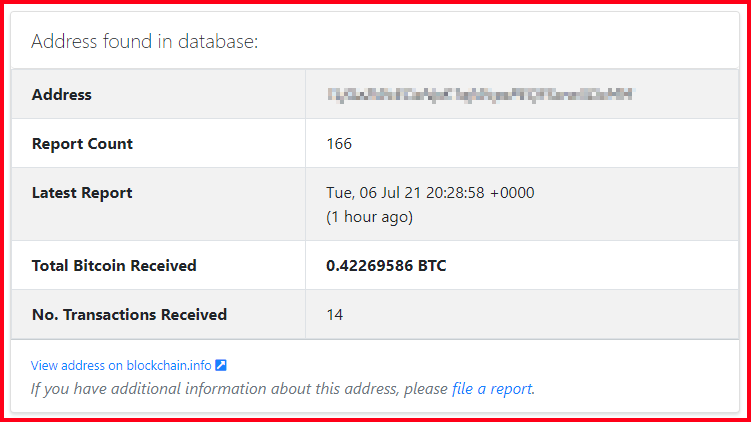
(2) Given that scammers nearly always ask for payment in Bitcoin – and Bitcoin is completely traceable (in terms of transactions – we just don’t know who controls any given Bitcoin wallet) – we can see how many people have fallen for each scam. It makes for interesting (and depressing) reading. I started monitoring one address recently – and over the space of a couple of weeks it had 14 deposits totalling NZ$20,476.13. That’s bad enough, but it’s just one of thousands of these scams. The bad guys send out millions of these eMails – and they only need a handful to fall for it to make it worth their while.
We can only hope that at some point in the future they will slip-up and authorities will be able to associate their anonimous Bitcoin wallet with the scammer in control of it … at which point every transaction is beautifully recorded as evidence for their prosecution. Sadly, the odds of this happening are slim … but I live in hope.
If you get one of these eMails – and are interested to see how many people have fallen for it – just copy/paste the wallet address into Google; chances are one on the first search suggestions will take you to a site called https://www.bitcoinabuse.com/ – it’s a wonderful site that lets people report scammer extortion attempts; be sure to log your own report and let others know about it too — there are far too many people giving their hard-earned money to scamming pr*cks; And no – they’re not sorry. Please – don’t fall for it. If in doubt give me a call – I’d be happy to take a look at whatever you’ve received – no charge.
Comments (0)